Security Research Case Study: Private Instagram Posts Authorization Flaw
This blog presents a cybersecurity research case study conducted to analyze how privacy controls are enforced on large-scale social media platforms. During this research, I identified an authorization flaw that caused private Instagram post data to be included in server responses under specific conditions.
Research Objective
The goal of this research was to evaluate server-side access control mechanisms and identify whether private user content was adequately protected against unauthorized requests.
Overview of the Privacy Issue
The issue was not related to login bypass or credential compromise. Instead, it was caused by inconsistent authorization checks at the backend level. In affected cases, private post metadata was embedded in server responses even when the requester was not authenticated.
Why This Is a Serious Security Concern
- Private user content relies entirely on server-side authorization
- Any inconsistency can expose sensitive data
- Client-side privacy indicators do not guarantee backend protection
High-Level Technical Explanation
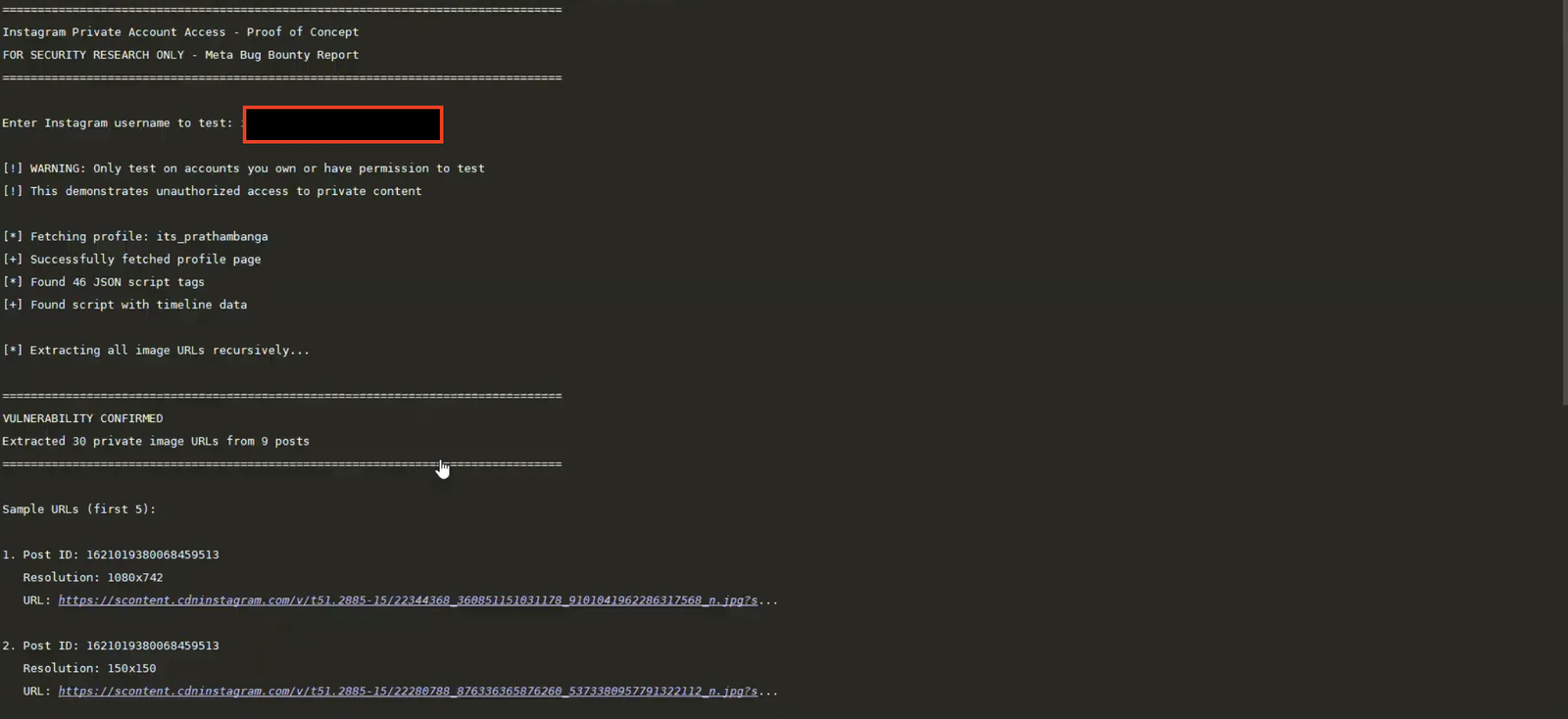
The research involved sending standard HTTP requests that mimicked legitimate client behavior. The server response was analyzed for embedded structured data. In certain responses, JSON objects containing private timeline data were found, indicating a backend authorization failure.
Code Analysis Summary (Research Perspective)
The proof-of-concept script used in this research performed the following actions:
- Requested a profile page without using authentication tokens
- Parsed HTML responses to locate embedded structured JSON
- Identified media-related objects intended for authorized users only
- Extracted URLs strictly for evidence validation
No automated exploitation, scraping, or unauthorized distribution was performed. All testing was conducted on accounts owned by the researcher or with explicit permission.
Impact Assessment
If abused, this flaw could have allowed unauthorized parties to access private media URLs, undermining user trust and platform privacy guarantees. This highlights how critical server-side authorization consistency is for user safety.
Responsible Disclosure
The issue was responsibly reported through official security disclosure channels. Following the report, the behavior was no longer observable, indicating that corrective measures were implemented.
Key Security Takeaways
- Authorization must always be enforced server-side
- Privacy settings should never depend on client logic
- All platform interfaces must share the same access controls
Conclusion
This research demonstrates how subtle backend authorization flaws can lead to major privacy risks. Continuous security testing and responsible disclosure are essential to maintaining trust in modern digital platforms.
Insta Private Exploit poc